spam email from friends: hacked or spoofed
Originally posted by Rich Pasco
Very often, I receive junk mail (spam) with a “From:” address of one of my contacts, for example a friend or fellow team member. The mail might contain an advertisement for Viagra or replica Rolex watches, a sad story about being robbed while on vacation (and please wire money), or just a link to a web site which could download malicious software onto my computer. In such cases, I delete that e‑mail without clicking on the potentially dangerous link.
Just as often, a friend or fellow team member contacts me stating that junk mail is going out in their name and asking what to do about it. Here is what I reply:
Hacked or Spoofed?
It is important to know whether your mail is hacked or spoofed. Let’s define these terms:
HACKED — Mail is actually being sent from your account by someone logged in to your server as you.
SPOOFED — Mail is being sent from somewhere else with your address being forged onto its “From:” line.
Continue Reading at www.richpasco.org
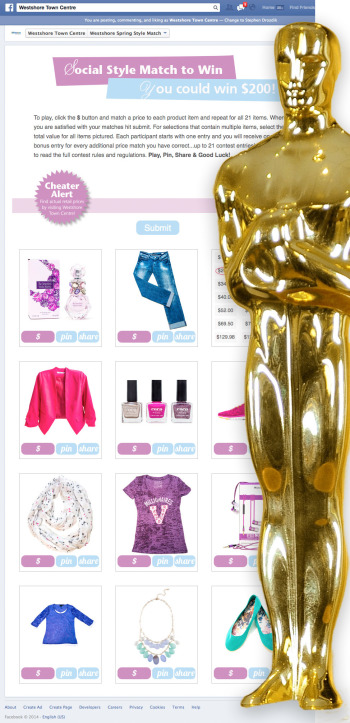
Facebook App Contest - Westshore Mall
Just launched — Facebook App Contest for Westshore Town Centre! Designed by Creating Excellence and programmed by Blender. This contest exists in the context of Facebook and runs in concert with Westshore’s in mall contest.
Noteworthy features include: mobile friendly, Like gate, Facebook login, Facebook sharing, Tweeting, Pinning.
This project brings together several technologies:
- Facebook SDKs to integrate into it’s social media network
- Pinterest + Twitter sharing
- Javascript + jQuery for interactivity
- PHP for server side coding
- MySQL for storing contest entries
Facebook applications are great ways to engage people with your brand or business. Visitors interact with you and can easily share out to their friends.
Choosing a Secure Password
Culture website BoingBoing has published a great article explaining how passwords can get cracked. Lot’s of easy to understand examples and best practices to keep you safe. (more…)
security: breaches remind us to take security seriously
Recently two major corporations have released information about security failures. Retailer Target released information that it’s point of purchase system had be hacked with estimates of up to 70 million customers’ personal data stolen by hackers. Starbucks was discovered to have been storing users passwords and information unencrypted in plain text in their iPhone app. The takeaway from both of these instances is your personal data is never secure and you must share it with caution.
Security breaches seem like every day events in out modern times. Rather than tune them out let them serve as reminders to take security seriously.
To be more secure online:
- never click on links in email unless you are confident they are safe, do not trust an email came from the address given
- wireless or public network allow for communications to be listened in on — check you have a secure SSL connection to the website you are visiting before sending any information (for instance logging in)
- assume poor security, always
One point I cannot stress enough: if you are using your email to log into a service with a password you commonly use you are at extreme risk.
improve search ranking with great content
One of the best ways to improve search ranking is to create great content. Great content that other websites will want to link to. It is especially good if the search engines consider these websites to be authorities on a topic you are targeting.
Recently the Blender website experienced just such a lift. Popular lifestyle blog Life Hacker linked to a tool hosted in the Blender website that calculated costs for a cloud storage service. Of course visitor traffic went through the roof increasing by several orders of magnitude when their post went live. More interestingly, search traffic both in the form of impressions (searchers seeing the Blender webpage in their search results) and visits nearly doubled. The content of my website hadn’t changed, but Blender looks a little better now. (more…)
internet security: Adobe hacked
Internet security is a continuing concern. This hacking attack is of interest to people who have registered copies of Adobe Photoshop, Lightroom, or other products. Your account at Adobe may have been compromised. If the password you used at Adobe is the same as you have used elsewhere then those accounts are also compromised. (more…)
more SEO Schema.org support from Google
Today on Google’s Webmaster Central blog they announced more search engine support for business / organization logos. Specifically they mentioned displaying suitable logos in search results. Having your logo included in a search engine results page (SERP) is a huge competitive advantage — or disadvantage if you don’t follow their suggestion!
You can read more about Rich Snippets and Schema.org as they relate to organization addresses in my previous blog post local SEO: first steps to better Vancouver results.
(more…)
SEO: image optimization with Shrink-O-Matic
Image optimization is an SEO factor. Google has stated in their Webmaster Guidelines that websites should be optimized to load quickly:
Monitor your site’s performance and optimize load times. Google’s goal is to give users with the most relevant results and a great user experience. Fast sites increase user satisfaction and improve the overall quality of the web (especially for those users with slow Internet connections), and we hope that as webmasters improve their sites, the overall speed of the web will improve.
Shrink-O-Matic is a free (donation) tool that can help with image optimization. This is a very handy tool for resizing images in bulk. As part of this process it strips out unnecessary information resulting in ‘lighter’ file sizes. The images aren’t as light as possible, but generally much improved. The ease of use of this tool makes it ideal for bulk image optimizing. Add resizing, renaming, and watermarking to the mix and you have a winner.
Shrink-O-Matic as an Adobe Air application so it should work on all platforms, as long as you have Air installed. If you find it useful I encourage you to make a donation to support author Quentin Thiaucourt’s work.
(more…)
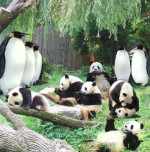
SEO tips: trouble with Google algorithm updates
Google regularly updates how they arrive at the search results provided to users. The process is part of the ever changing search landscape; SEOs tweak for best Google positioning and Google tweaks for best search results. You can view a list of Google’s algorithm updates at SEOMoz, a SEO tools provider. Two recent Google algorithm updates have had a particularly significant effect: code named Panda and Penguin.
For Google’s search results to be relevant it has to correctly identify the best answers to user searches. Google works hard in this regard, sometimes with transparency and sometimes not. To it’s credit Google has published Google Webmaster Guidelines for designers and SEOs outlining best practices. To quote Google (emphasis mine):
Avoid tricks intended to improve search engine rankings. A good rule of thumb is whether you’d feel comfortable explaining what you’ve done to a website that competes with you, or to a Google employee. Another useful test is to ask, “Does this help my users? Would I do this if search engines didn’t exist?”
…
Avoid the following techniques: Automatically generated content, Participating in link schemes, Cloaking, Sneaky redirects, Hidden text or links, Doorway pages, Scraped content, Participating in affiliate programs without adding sufficient value, Loading pages with irrelevant keywords
All of the techniques Google mentions have at one time or another been common practice to either promote websites or create website content. (more…)